Ethical Hacking and Pentesting Hacking News Information Security Reporting Software Security
A True Hacking Story: How I Hacked Microsoft’s Kiosks Systems Remotely and Get All Employee Information…

Approximately 3 months ago, I had success to access a number of information from Microsoft employee who works across the globe with the vulnerabilities I identified in two different Kiosk systems from Microsoft.
Dislclaimer:
The information below is for training and information purposes only. It was written to reveal the situation caused by a simple error made by a software developer.Murat Kaya a.k.a mksecurity
You hereby acknowledge that if you damage the Microsoft system using the information contained herein, you are solely responsible for all legal and ethical liability.
TL;DR;
Yes, as i said before, everything is started almost 3 months ago…
With this vulnerability I found that, there were a number of processes that could be done remotely from the kiosks in one or more of Microsoft’s buildings.
With one of them, I was able to set up a meeting with Satya and Bill Gates, and I was able to print a meeting card from the kiosk and get an appointment … (I don’t know if the card is really out or I’m not there. :))
The first kiosk system, as I understand it, is working for a meeting or interview request and set, while the other kiosk system works for a business that can monitor the activities on Microsoft campuses. Even the position of your vehicle could be obtained through this kiosk.
I have written this article to draw attention to the fact that no matter how big you are, the weakest link is the people himself and i wanted you to see how the huge Microsoft’s data could be captured because of a really careless software engineers.
Everything started with a simple search Word…
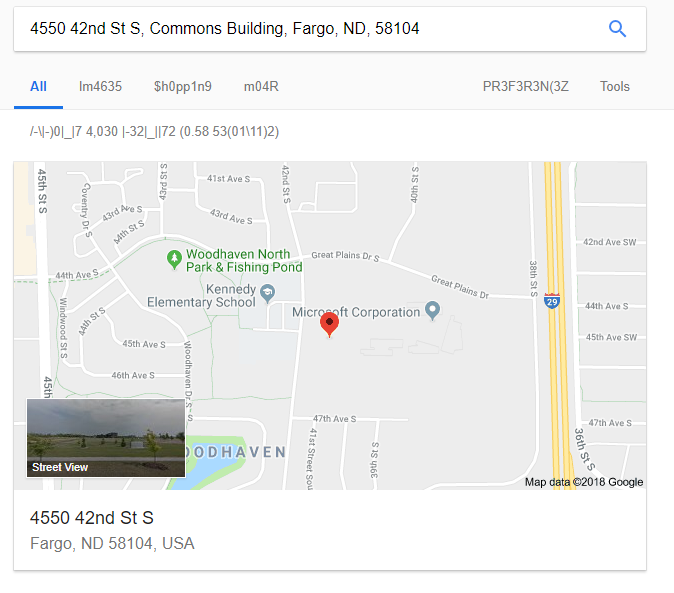
A search field is located on the top right when you enter the Microsoft.com website as usual.
With this I deliberately searched for a pattern in the form of like “11111111-1111111…”.
If you ask me why I’m searching this kind of pattern,because, the data I entered was actually a TOKEN format, and it was generally a default token on many system for testing purposes. (11111111-1111-1111-1111-111111111111 this is exactly the case)
I have to be quite lucky because have got a lot of information as listed below. At first, I was excited to see the “prod” in the domain, eventhough it meant nothing to me : =)
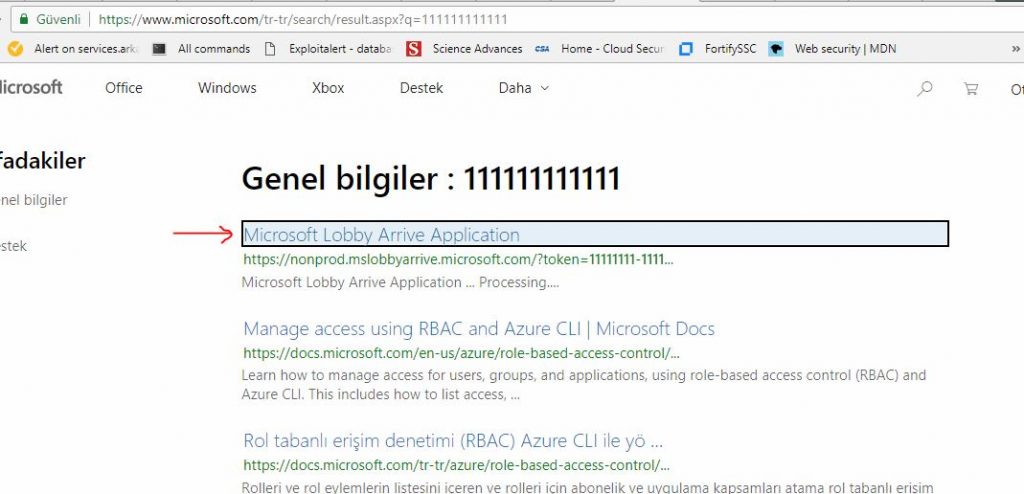
** Normally this site is not supposed to be here, but “Sharepoint” has also included this site index.
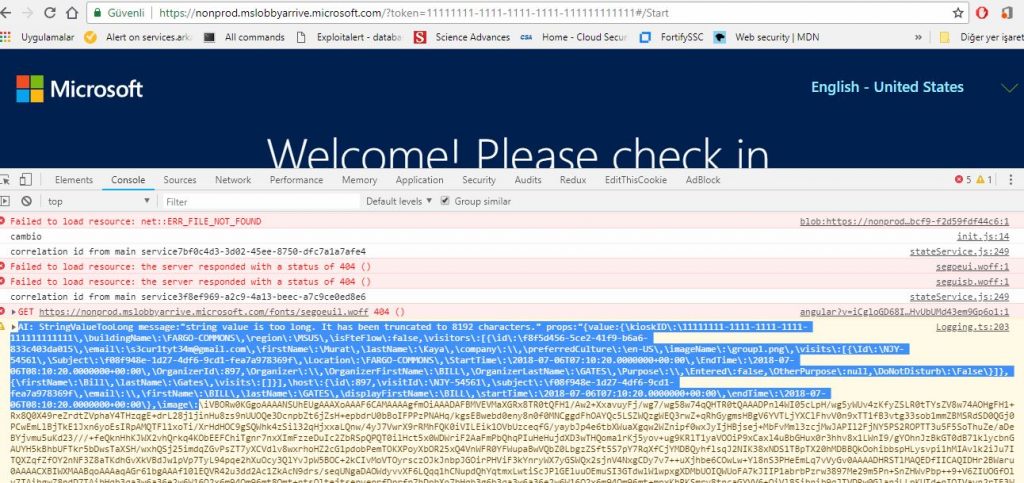
Without waiting more than just clicked on the link and ascreen greeted me as follows;
Obviously my excitement increased because I just clicked on a link that gave me Microsoft employee information (Did you mean?)
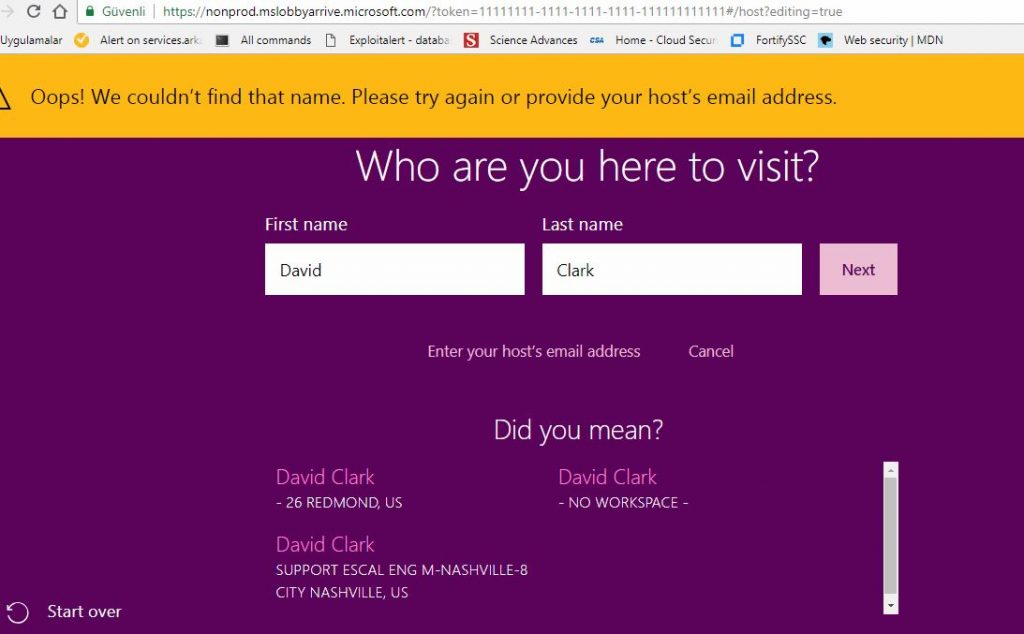
I looked at the source code of the page without wasting anytime (I thought the security analysts could see that I was running this queryand acted as fast as possible)
All the fatal errors a developer could do were all collected on a single page.
Now, I could easily tamper with other systems along with the information here …
First of all, I have logged all my data communication by inserting a proxy, calling all pages, APIs, javascript files etc. backed up to my system. Because if the back structure was huge, I detected hundreds of files and api calls.
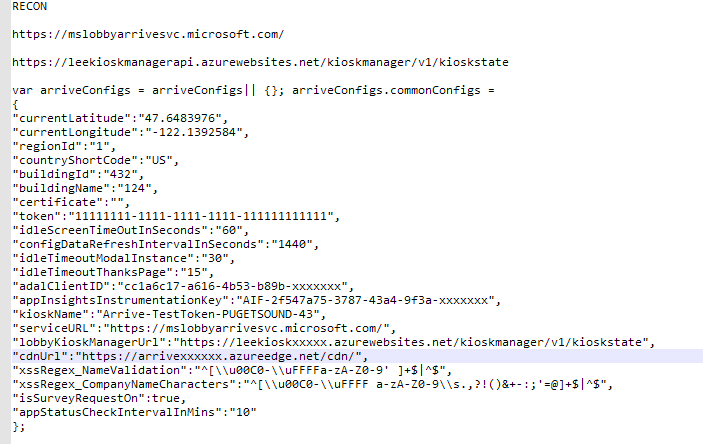
I had access to a different kiosk and api, so I found thegold mine I was looking for after a while.
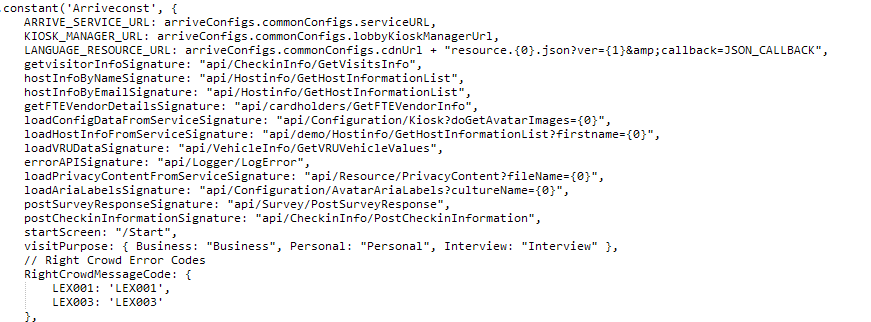
The above list was used to access other kiosk systems. In other words, I could easily access other kiosk api that I had obtained and it was. I started to tamper with the following api endpoints, which I thought could provide vital information with the information I obtained here.
I started testing a few api accesses I selected from thelist below.
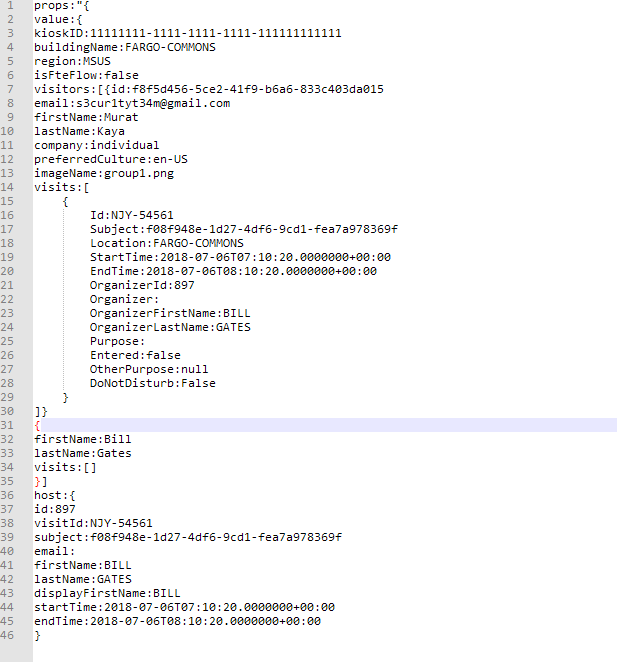
First, I questioned the employee information api (GetHostInformation), and I chose someone who was already a consultant from a familiar name. (To understand whether the system is really working with up-to-date data)
After all, CEO Satya, of course everyone knows.
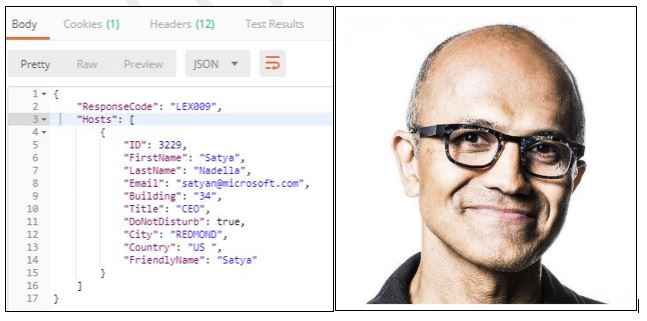
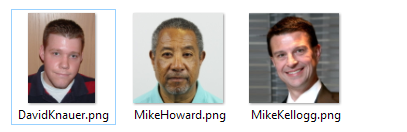
While I was dealing with all of this, a bug in the browser caught my attention. The developer logged the errors directly to the console, and when I examined the error, I noticed that all the information of the user was in error. The best one was the photo data encoded with “Base64”.
As you can see below, almost all of the information is available in the console.
Decode the base64 image file and extract it as a photo. Youcan see some of the photos I have obtained according to some search results(some of them are familiar :))
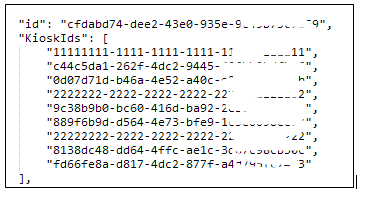
As I went deeper into a different kiosk, this kiosk wasdifferent from the others. Activities related to Microsoft campus etc. Normally when you want to log in to the system you were instantly redirected to Microsoft login global page, “but again”, the developer has made a fatal error by using “Javascript location.href” instead of 302 redirect!
It was very easy to get over this, I just pressed the STOPbutton on the browser and I could see the code of the page before it wasoriented with the view source. There was a lot of gold…
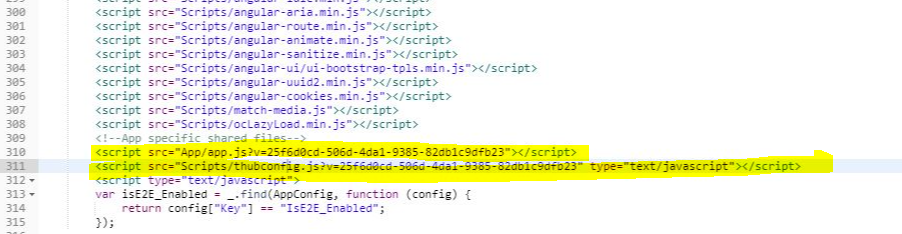
The software engineer, relying on routing, had stored the app config information in the site. When I looked at these files, I reached different api endpoints and information.
Similar to the previous one, Token information, api endpoints, bing map accessinformation, Luis chatbot access information, such as had a lot of private data.
Thub configs
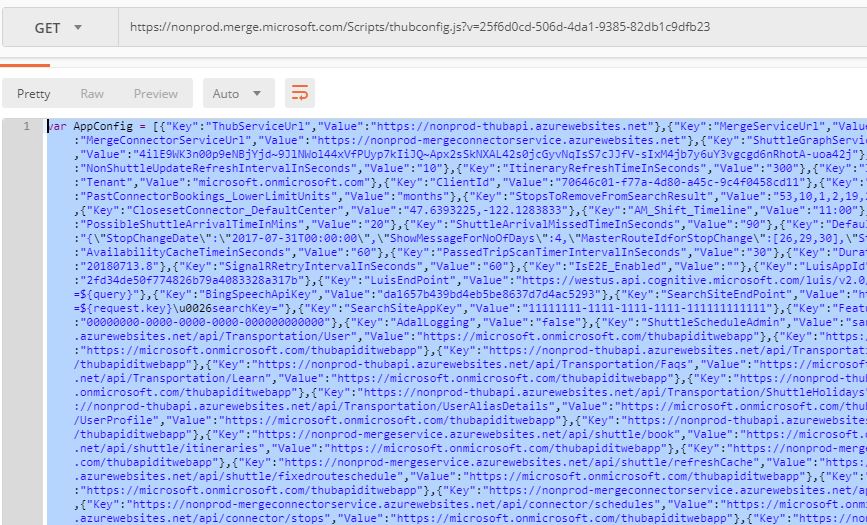
App configs

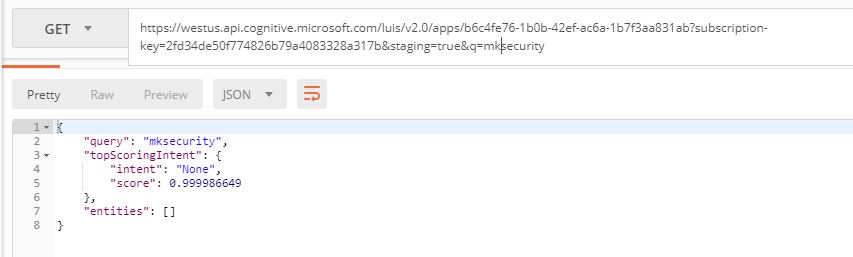
Without wasting much time, I started to send queries torelevant endpoints to see if this information was valid. I tried a similarquery with Luis, so the key was valid, I repeated a similar query for the Bing map service for other services. They were all active and valid.
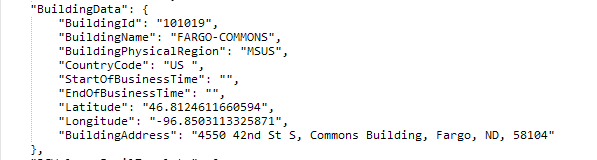
The result of the api giving information about the building;
I’ve noticed that I can access the AppInsight logs oncemore. I have all the tokens needed for system access. When I query for AppInsight, the data came as follows;
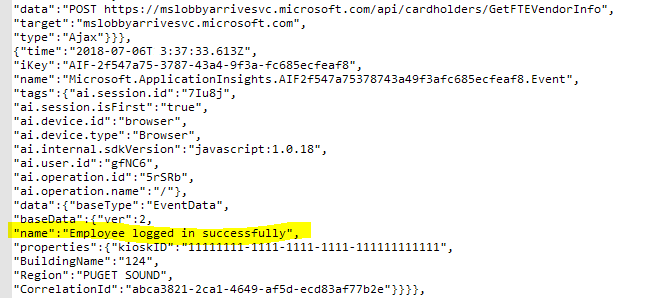
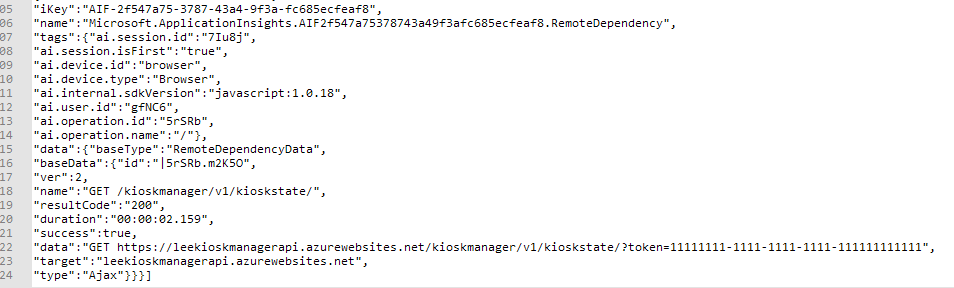
Lobby raw logs obtained from AppInsight (more)
Considering that I have proven that all other endpoints and kiosk systems are accessible; I contacted Microsoft Security Team.
I had to do all the steps I told you above for 2 days, until the morning, step by step. They finally accepted all of the security gaps, and announced that they would start work on closure.
They said they had closed the gaps after the PoC and thefinal tests and would publish my name on the “Microsoft Security Researcher” list. I guess this was the most enjoyable part.
Link: https://www.microsoft.com/en-us/msrc/researcher-acknowledgments-online-services-archive?rtc=1
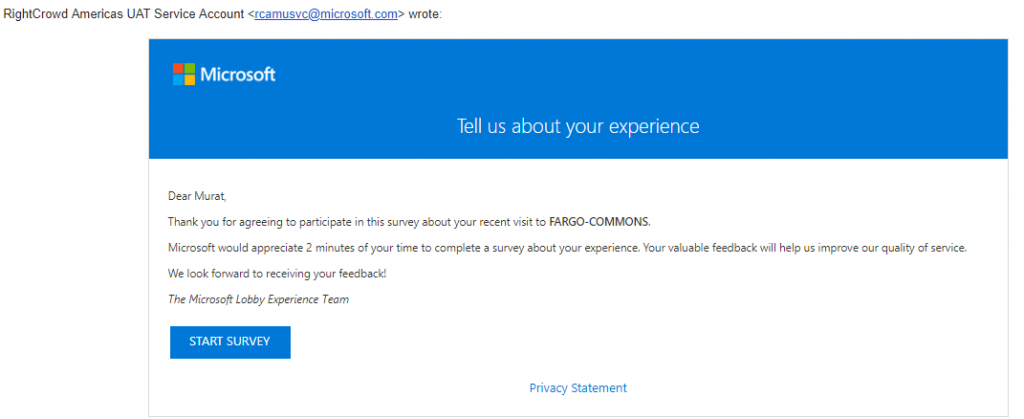
Below, you can see one of the mails that asked me if I had a good time with Bill Gates and Satya in Microsoft’s office (Of course there was no such thing :))
BONUS
Registered on the kiosk, the data of my appointment with Bill Gates.
Thanks for reading…



POST YOUR COMMENTS
You must be logged in to post a comment.